mirror of
https://github.com/jellyfin/jellyfin.git
synced 2026-05-04 18:09:12 +03:00
Security issue when browsing libraries #396
Reference in New Issue
Block a user
Delete Branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @quentinus95 on GitHub (Feb 7, 2019).
Originally assigned to: @joshuaboniface on GitHub.
Hi,
I'm not (yet) using Jellyfin, but there was a security issue in Emby I pointed out almost one year ago.
Does the issue still exist in Jellyfin? It is pretty serious in my opinion.
https://github.com/MediaBrowser/Emby/issues/3270
Thanks!
@joshuaboniface commented on GitHub (Feb 7, 2019):
Ooh that is a heck of a security hole. I don't think we've explicitly fixed it, but will take a look.
@bobberb commented on GitHub (Feb 7, 2019):
oh, who knew my requested feature of "public share links" was here the whole time @joshuaboniface 🤣
@JustAMan commented on GitHub (Feb 8, 2019):
Don't worry, we'll fix it so it won't work @bobberb ;)
@hawken93 commented on GitHub (Feb 9, 2019):
I think Luke's thing in that thread and fixing this hole could be done by passing on auth to the target device instead of making a big gaping hole and having a relatively short timeout on that. Does this mean that the chromecast working at all is because of this? Lol
@JustAMan commented on GitHub (Feb 9, 2019):
I am not sure I support Luke idea of allowing admin to cast to target device no matter who is logged there...
Though we can still support that use case if we properly support temporary links to media, like @bobberb asks.
@hawken93 commented on GitHub (Feb 9, 2019):
How does the chromecast authenticate?
@cvium commented on GitHub (Feb 9, 2019):
It uses the user's auth token
@hawken93 commented on GitHub (Feb 11, 2019):
Aha, then I agree with @justaman. Sharing links could be used with some kind of share token :)
@bobberb commented on GitHub (Feb 11, 2019):
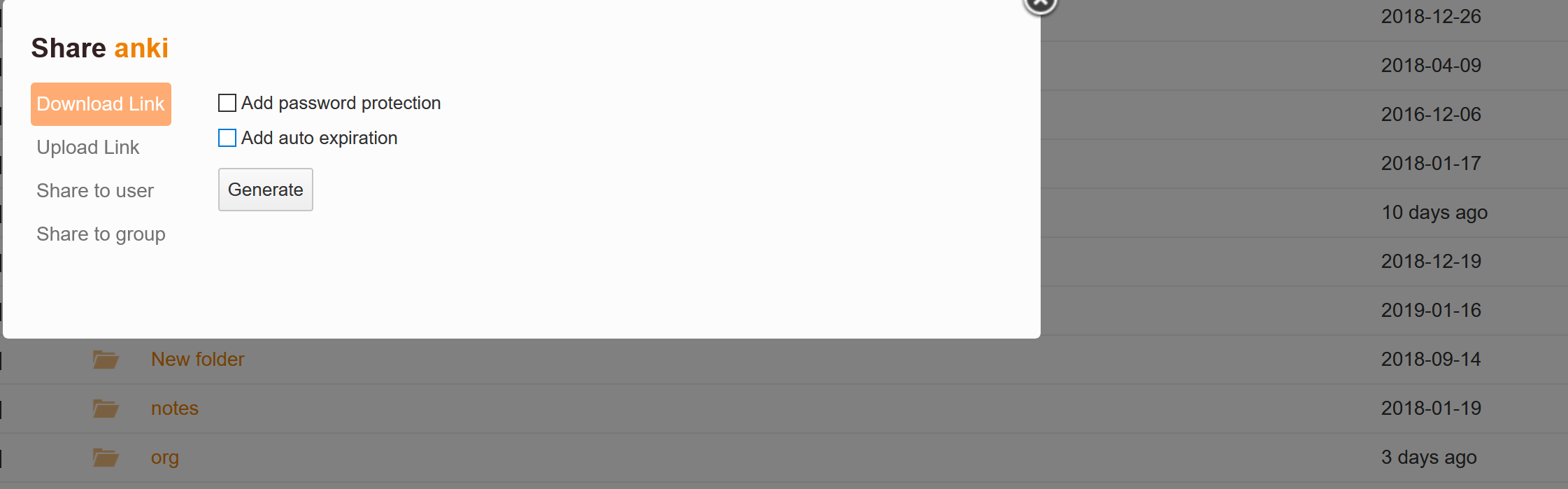
tokens a la seafile +/- expiry times?
@JustAMan commented on GitHub (Feb 11, 2019):
Something along this lines, yes.
@Tolriq commented on GitHub (Feb 18, 2019):
I do not follow actively this project, but be aware that this will require proper thinking for many cases.
Typically you can send http header when streaming to UPnP devices and many other cases. Protecting the media require proper thinking and documentation as you'll break things on the road (Including my app :p)
Plex support passing the token via url get params, don't know if Emby/JellyFin also support that, but it would be mandatory to support both headers and a GET param to be able to support all the players currently usable.
@dkanada commented on GitHub (Apr 10, 2019):
I think we support this in some capacity already because the log pages are sent with the token in the query strings. Not sure how often it gets used but seems like the ideal solution in most cases, excepting the public share feature listed above.
@joshuaboniface commented on GitHub (Apr 16, 2019):
Well, good news - I can't seem to reproduce this!
I followed the steps you outlined:
In both cases, nothing happened - no errors, but also no unexpected access to the library.
I think based on this that we're good here - when and how it was fixed I'm not sure, but it does seem to be. If you can verify that would be appreciated, otherwise we can close this one out!
@joshuaboniface commented on GitHub (Apr 20, 2019):
Closing based on my testing above - if this still occurs and can be replicated please let us know!